
Security is getting more difficult to attain nowadays on the old interwebs, and for good reason. It's not about hackers getting more clever, like we see in Mr. Robot, but more about companies getting a bit lazier. It's about not having the correct standards in place, and mainly the fact that humans work at the companies where your password is stored. If we want total security, we'd need companies like LinkedIn to be solely run by autonomous beings, which is a post for another time. But, things are looking up, and there are newer security measures being developed that can aid in strengthening your online fingerprint.
2 Factor Authentication
2 Factor Authentication helps secure your accounts online by adding a second component to your login process. And that is a randomly generated token that has a short life and is sent directly to you through another medium, such as alternate email or your phone through SMS.
2 Factor Authentication should be the defacto standard when creating an account on a website. Assuming the website offers it of course. Today only the larger organizations such as Google, Yahoo and LinkedIn offer it as an option.
It's Not Perfect
While you should definitely set up 2FA whenever possible, it's not without its shortcomings. For one, this doesn't stop hackers from stealing passwords on websites. 2FA does little to prevent the +100 million passwords that were taken from LinkedIn a few years ago. Those emails and passwords are still out there in the wild. Many of those, open up other doors as well, as most people tend to use the same passwords for multiple websites.
Secondly, phone based 2 factor authentication has more noticeable problems, and that is that it is tied to your phone number. This isn't a concern let's say if you decide to cancel your cellphone plan and get a new number, because the new owner of the number won't have any idea what the generated token means or where it goes. But as of late, it does seem like some malicious individuals are attempting to spoof SIM cards in an attempt to get these generated tokens and take control of people's accounts. And that's because, with phone based 2 factor authentication, the flow is still out of your hands. It has to go to your phone company, which will forward you the SMS. And that little stop, can cause some issues.
Universal 2nd Factor (U2F)
And now let's welcome U2F. U2F is a relatively new open security standard maintained by the FIDO Alliance and created by Google and Yubico. Their main goal is to provide a more secure second factor authentication method through the use of public key cryptography and biometric or other external feedback. U2F uses a USB dongle that helps to sign a request using a private key that it stores locally, that can be written to, but not read from. And as of late, more and more companies are jumping on board and integrating it into their own sites. It's also getting better and better as the standard matures. For example, in 2015 the FIDO Alliance added new transport protocols for mobile devices using NFC.
The YubiKey
One of the cheapest alternatives in the world of U2F, is the YubiKey, which is, created by Yubico, of course. It is a small USB like dongle that you can use in any USB port, and when prompted will handle the public/private key relation with a supporting application or browser. For example, if you log in to Google through an updated version of Chrome that supports U2F, you will asked to present your YubiKey after you enter your password. One simple touch of the device will begin the encryption challenge, and when approved you are in. And there are several reasons why this is the way to go when dealing with online security.
U2F Benefits
The Yubico Security Key is made up of injection molded plastic encasing the circuitry and the exposed parts are made up of military grade hardened gold. It requires no internal power to operate and it doesn't require any drivers. It simply just works.
One of the strongest benefits of this is that it relies on something that belongs to you and is in your pocket. A hacker a world away wouldn't be able to copy any of your private keys, as they are stored locally on the YubiKey in order to log in to a website. As oppose to the current conventional phone/SMS method, which relies on a phone number that can sometimes be spoofed if an intruder wants it bad enough. Or even a secondary email token, that is susceptible to the same.
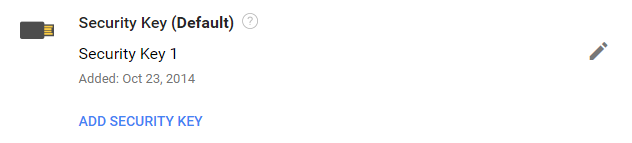
You can also have multiple keys assigned to a single service provider making it that much more secure. Which brings me to my last point. You can lose your YubiKey and you will be just fine. There is no descriptive data to associate you with the device and the private keys cannot be read from the device. And this anonymity is what makes the U2F standard so powerful. Currently, many of the sites that you use on a daily basis either for work or at home support U2F authentication. A few examples are Google, BitBucket, Facebook and Dropbox, just to name a few. Even Windows supports security using the YubiKey now.
It's definitely a new paradigm in the way that we treat security. We've gotten so used to memorizing characters during the past few decades that anything else seems a bit odd. We use pins for our ATM's and we use passcodes to enter locked doors. But maybe it's time that we take that responsibility out of our hands.
Walt is a software engineer, startup founder and previous mentor for a coding bootcamp. He has been creating software for the past 20+ years.